In this article
I have been writing some blogs entries (and even a Microsoft KB) about c2WTS, but the subject never exhausts. I was helping two different customers to troubleshoot issues with SharePoint Excel Services. In one of the cases the problem happened randomly and the error message was saying that the request to the external data (SQL) had failed because the request did not include a valid Kerberos header, but no reference to c2WTS in the ULS logs.
The other case was that some users could access Excel Services while others could not, this time there was an error in ULS logs pointing to access denied in c2WTS. Without explaining the internals of these two cases, one can say that in both cases c2WTS was working as expected but some other factor was impairing its use with SharePoint.
Before pointing at c2WTS as culprit of some SharePoint access error, look for these three tags in the ULS logs: g8g7, fvx8 or bz7l in Claims Authentication category (Medium).
This ULS entry would look like this:
07/14/2011 14:33:34.03 w3wp.exe (0x1144)0x1960 SharePoint Foundation Claims Authentication bz7l Medium
SPSecurityContext.WindowsIdentity: Could not retrieve a valid windows identity for NTName=’CONTOSO\jdoed’, UPN=’jdoed@contoso.com’. UPN is required when Kerberos constrained delegation is used. Exception: System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. Server stack trace:
at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter)
at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc)
at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout)
at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation)
at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message) Exception rethrown
at [0]:
at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg)
at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation)
at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity().
SharePoint uses c2WTS to transform a claim identity into a valid Windows Identity Token. You cannot (for now) send a request to SQL Server or other data sources passing the claim. So, for internal users in Active Directory the claim will be mapped to a Windows Identity Token and that token will be used to access the resource. Since c2WTS only requires the UPN to generate a token, by default no one can access the service. To allow access you have to edit the .config file to add the groups and users to the allowed callers section.
SharePoint installs c2WTS as part of its pre-requisites as c2WTS is actually part of Windows Identity Foundation SDK. The configuration happens when you add the correspondent service in the farm. If everything is alright the service will be configured to start automatically (read my previous post on dependencies) under SYSTEM\NT AUTHORITY and will add the SharePoint local group WSS_WPG to the list of allowed groups in c2WTS. When adding SharePoint Excel Services, the domain account provided needs to be able to create Windows tokens in the c2WTS machine (the service only works with local requests) and it will be added automatically to WSS_WPG by SharePoint (you don’t have to do this). All this actions are necessary since once accessing the service you can impersonate a user by simply supplying the UPN claim. The input is the UPN string. The return is the (limited) Windows Token or an error.
Testing c2WTS configuration is not possible without some code. You have to be logged (or impersonating) an account that has rights to c2WTS. I suggest the account you used for Excel Services. To test using the same method that SharePoint does, you only need to call this static class in c2WTS:
WindowsIdentity wi = S4UClient.UpnLogon(“rviana@contoso.com”);
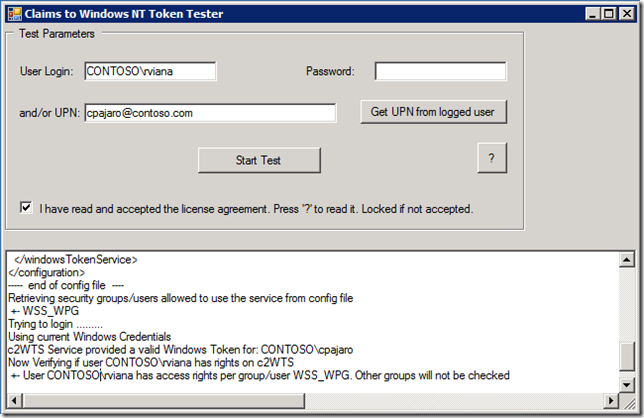
This static method will use WCF net.pipe (only local) to communicate with the real c2WTS service (I blogged about net.pipe and real pipes in a previous post). The full test of the complete configuration is a bit more complex. I have put together a sample application to perform all tests I could remember. The App looks like:
Quick Instructions:
Start the Application as Administrator. If you want to impersonate Excel Account, change “User Login” to enable the Password field. By default the user will be the account running the application. If you want to continue with the interactive user, you will not need to enter password. For UPN you can enter any valid UPN claim (normally user@domain), if you want to test your own account you can choose to get UPN from logged user. If you want to impersonate another user or test if the current user can obtain tokens, please enter the UPN manually.
Full Result:
| Testing Service c2WTS+- Service c2WTS found+- Service c2WTS is running+- Path of service: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe+- Config File: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe.config+- Service Logon: SYSTEM\NT AUTHORITY—– start of config file —-<?xml version=”1.0″?><configuration><configSections><section name=”windowsTokenService” type=”Microsoft.IdentityModel.WindowsTokenService.Configuration.WindowsTokenServiceSection, Microsoft.IdentityModel.WindowsTokenService, Version=3.5.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35″ /></configSections><startup><supportedRuntime version=”v4.0″ /><supportedRuntime version=”v2.0.50727″ /></startup><windowsTokenService><!–By default no callers are allowed to use the Windows Identity Foundation Claims To NT Token Service.Add the identities you wish to allow below.–><allowedCallers><clear /><add value=”WSS_WPG” /></allowedCallers></windowsTokenService></configuration>—– end of config file —-Retrieving security groups/users allowed to use the service from config file+- WSS_WPGTrying to login ………Using current Windows Credentialsc2WTS Service provided a valid Windows Token for: CONTOSO\cpajaroNow Verifying if user CONTOSO\rviana has rights on c2WTS+- User CONTOSO\rviana has access rights per group/user WSS_WPG. Other groups will not be checked*** Analysis Complete *** |
You can download source and EXE here.
Please notice that since this is supposed to mimic SharePoint 2010, the App is 64-bits. Also be aware this application is provided “AS IS” with no guarantees. You need to accept the license to use it.
Comments
-
Anonymous
July 26, 2012
How do you diagnose failures to call the service? My user .administrator is a member of WSS_WPG and has local policy settings to act as part of the operating system and impersonate users. I still get an access denied on the c2WTS service.
can you point me in the right direction on where i can go to find out more about how to get past this?
Thank you!
Testing Service c2WTS
+- Service c2WTS found
+- Service c2WTS is running
+- Path of service: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe
+- Config File: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe.config
+- Service Logon: SYSTEMNT AUTHORITY
—– start of config file —-
<?xml version=”1.0″?>
<configuration>
<configSections>
<section name=”windowsTokenService” type=”Microsoft.IdentityModel.WindowsTokenService.Configuration.WindowsTokenServiceSection, Microsoft.IdentityModel.WindowsTokenService, Version=3.5.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35″ />
</configSections>
<startup>
<supportedRuntime version=”v4.0″ />
<supportedRuntime version=”v2.0.50727″ />
</startup>
<windowsTokenService>
<!–
By default no callers are allowed to use the Windows Identity Foundation Claims To NT Token Service.
Add the identities you wish to allow below.
–>
<allowedCallers>
<clear />
<add value=”WSS_WPG” />
</allowedCallers>
</windowsTokenService>
</configuration>
—– end of config file —-
Retrieving security groups/users allowed to use the service from config file
+- WSS_WPG
Trying to login ………
Using current Windows Credentials
***** c2WTS could not provide a valid Windows Token. Reason: Access is denied.
Server stack trace:
at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter)
at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc)
at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout)
at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation)
at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message)
Exception rethrown at [0]:
at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg)
at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation)
at c2WTSTest.Form1.button2_Click(Object sender, EventArgs e)
Now Verifying if user MYWORKLAPTOPAdministrator has rights on c2WTS
+- User MYWORKLAPTOPAdministrator has access rights per group/user WSS_WPG. Other groups will not be checked
*** Analysis Complete *** -
Anonymous
July 26, 2012
Hi feemurk,
You need an AD user from the same domain you want to resolve the UPN and acquire the Windows token. A local user will not do the trick.
See:
blogs.msdn.com/…/step-by-step-configuration-of-excel-calculation-services-ecs-when-using-kerberos.aspx
and:
msdn.microsoft.com/…/cc949014.aspx
Let me know if I answered your question. -
Anonymous
December 02, 2012
Dear Rodney,
Any ideas why c2wts may be tempremental? For me it works for a few minutes after restart and then gets tired, fed up and packs in completely: stop resolving UPNs into valid tockens displaying the error message in your blog. Almost after every restart the behaviour repeats. Any ideas at all will be very much appreciated!
Thank you,
Kindest regards,
Dmytro
dmytro.andriychenko@sage.com -
Anonymous
December 02, 2012
Dear Rodney,
Any ideas why c2wts may be tempremental? For me it works for a few minutes after restart and then gets tired, fed up and packs in completely: stop resolving UPNs into valid tockens displaying the error message in your blog. Almost after every restart the behaviour repeats. Any ideas at all will be very much appreciated!
Thank you,
Kindest regards,
Dmytro
Dmytro.Andriychenko@sage.com -
Anonymous
December 03, 2012
Hi Dmytro,
If you let me know more details about the problem I might be able to give you some ideas. Is it happening in the same server all the time? Are you using any customization? How are you using c2WTS with SharePoint? Do you have the same application pool identity across all servers? Is it failing when resolving the same UPN?
What is the stack you are seeing in the ULS logs?
Thanks,
Rodney -
Anonymous
December 05, 2012
Thank you ever so much for getting back to me.
I have a single Sharepoint Application Server, so it is only that one I have ever tested it on. I never tried to test it on any other servers as I did not see the point – happy to do it if it may shed some light on the problem.
The c2wts is running under an AD user (ADOMAINSA_BI_c2wts) identity with Constraint Kerberos Delegation enabled and “Trusted to Authenticate for Delegation User Access Control” bit set.
This is the output of your program for the c2wts account trying to resolve my own UPN into a valid tocken (I have removed most of the content of the config file to fit within the post):
Testing Service c2WTS
+- Service c2WTS found
+- Service c2WTS is running
+- Path of service: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe
+- Config File: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe.config
+- Service Logon: SA_BI_c2wtsADOMAIN
*** Service MUST BE ‘SYSTEMNT AUTHORITY’ ***
—– start of config file —-
…
<allowedCallers>
<add value=”WSS_WPG” />
</allowedCallers>
…
—– end of config file —-
Retrieving security groups/users allowed to use the service from config file
+- WSS_WPG
Trying to login ………
Using provided credentials to login
***** c2WTS could not provide a valid Windows Token. Reason: Access is denied.
Server stack trace:
at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter)
at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc)
at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout)
at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation)
at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message)
Exception rethrown at [0]:
at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg)
at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation)
at c2WTSTest.Form1.button2_Click(Object sender, EventArgs e)
Now Verifying if user ADOMAINSA_BI_c2wts has rights on c2WTS
+- User ADOMAINSA_BI_c2wts has access rights per group/user WSS_WPG. Other groups will not be checked
*** Analysis Complete *** -
Anonymous
December 05, 2012
The comment has been removed -
Anonymous
December 05, 2012
This is the error message displayed by PowerView when trying to acccess a tabular instance (most informative part of it):
Cannot impersonate user for data source ‘EntityDataSource’.
<Message msrs:ErrorCode=”rsClaimsToWindowsTokenError” msrs:HelpLink=”go.microsoft.com/fwlink xmlns:msrs=”www.microsoft.com/…/reportingservices”>Cannot convert claims identity to windows token.</Message> -
Anonymous
December 05, 2012
This is the ULS entry for the same error in PowerView (similar messages can be seen for ExcelServices Authentication, when they fail, they fail together for the same reason):
12/06/2012 12:30:14.58 w3wp.exe (0x0AA4) 0x1850 SharePoint Foundation Claims Authentication bz7l Medium
SPSecurityContext.WindowsIdentity: Could not retrieve a valid windows identity for NTName=’ADOMAINName.Surname’, UPN=’Name.Surname@ADOMAIN.COM’. UPN is required when Kerberos constrained delegation is used. Exception: System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. Server stack trace: at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter) at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc) at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout) at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMesage methodCall, ProxyOperationRuntime operation) at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation) at Microsoft.SharePoint.SPSecu… c3bc654f-f80b-4670-8a81-c4e2709843f3rityContext.GetWindowsIdentity().; c3bc654f-f80b-4670-8a81-c4e2709843f3 -
Anonymous
December 05, 2012
This is the next entry in the log:
12/06/2012 12:30:14.58 w3wp.exe (0x0AA4) 0x1850 SQL Server Reporting Services Report Server Web Server 0000 Unexpected
Throwing Microsoft.ReportingServices.Diagnostics.Utilities.ClaimsToWindowsTokenException: , Microsoft.ReportingServices.Diagnostics.Utilities.ClaimsToWindowsTokenException: Cannot convert claims identity to windows token. —> System.InvalidOperationException: Could not retrieve a valid Windows identity. —> System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. Server stack trace: at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter) at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc) at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOpera… tionRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout) at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation) at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation) at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity() — End of inner exception stack trace — at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity() at Microsoft.ReportingServices.ServiceRuntime.WcfUserContext.GetWindowsIdentity() — End of inner exception stack trace —; c3bc654f-f80b-4670-8a81-c4e2709843f3 -
Anonymous
December 05, 2012
And the next one is this:
12/06/2012 12:30:14.58 w3wp.exe (0x0AA4) 0x1850 SQL Server Reporting Services Report Server Processing 0000 Unexpected
Throwing Microsoft.ReportingServices.ReportProcessing.ReportProcessingException: , Microsoft.ReportingServices.ReportProcessing.ReportProcessingException: Cannot impersonate user for data source ‘EntityDataSource’. —> Microsoft.ReportingServices.Diagnostics.Utilities.ClaimsToWindowsTokenException: Cannot convert claims identity to windows token. —> System.InvalidOperationException: Could not retrieve a valid Windows identity. —> System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. Server stack trace: at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter) at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc) at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout) at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation) at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation) at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity() — End of inner exception stack trace — at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity() at Microsoft.ReportingServices.ServiceRuntime.WcfUserContext.GetWindowsIdentity() — End of inner exception stack trace — at Microsoft.ReportingServices.ServiceRuntime.WcfUserContext.GetWindowsIdentity() at Microsoft.ReportingServices.Diagnostics.ImpersonationContext..ctor(UserContext userContext) at Microsoft.ReportingServices.Diagnostics.DataExtensionConnectionBase.HandleImpersonation(IProcessingDataSource dataSource, DataSourceInfo dataSourceInfo, String datasetName, IDbConnection connection, Action afterImpersonationAction) — End of inner exception stack trace —; c3bc654f-f80b-4670-8a81-c4e2709843f3 -
Anonymous
December 05, 2012
I have replaced the actual user with Name.Surname and domain name with ADOMAIN throughout. -
Anonymous
December 05, 2012
Please let me know if I can provide any more information on the matter.
Just to add context, this domain was previously running with 2003 DC running at 2000 mixed mode functional level. Then the functional level was increased to 2003, new 2008 R2 DC was added, synched up with the old DC and then brought to 2008 R2 functional level. After that the old DC was ditched and the new took the IP and the name of the old one.
I canot tell you if we had the same problem with c2wts throughout this journey, only that we have them now.
I have followed links on your blog and made sure the Read permission in AD Security settings are set for the users involved for all Authenticated Users, but that did not seem to change anything.
Any Ideas to try will be very much appreciated, I am a bit stuck, to be honest, not even sure where to keep looking…
Thank you very much in advance,
D -
Anonymous
December 10, 2012
Could not really resolve the problem, instead changed the identity of c2wts service back to Local System and reconfigured delegation for the application server to enable delegation to all the right places. Once there, everything worked a charm. Thanks to Christopher Scolt http://www.scolts.com/?p=56 for a tip on how to reset c2wts identity within SharePoint back to Local System. Please note, you will then have to actually change the service identity in services.msc and restart c2wts. -
Anonymous
January 01, 2013
Hello Rodney
Your utility gave following information:
Testing Service c2WTS
+- Service c2WTS found
+- Service c2WTS is running
+- Path of service: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe
+- Config File: C:Program FilesWindows Identity Foundationv3.5c2wtshost.exe.config
+- Service Logon: SYSTEMNT AUTHORITY
—– start of config file —-
<?xml version=”1.0″?>
<configuration>
<configSections>
<section name=”windowsTokenService” type=”Microsoft.IdentityModel.WindowsTokenService.Configuration.WindowsTokenServiceSection, Microsoft.IdentityModel.WindowsTokenService, Version=3.5.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35″ />
</configSections>
<startup>
<supportedRuntime version=”v4.0″ />
<supportedRuntime version=”v2.0.50727″ />
</startup>
<windowsTokenService>
<!–
By default no callers are allowed to use the Windows Identity Foundation Claims To NT Token Service.
Add the identities you wish to allow below.
–>
<allowedCallers>
<clear />
<add value=”WSS_WPG” />
</allowedCallers>
</windowsTokenService>
</configuration>
—– end of config file —-
Retrieving security groups/users allowed to use the service from config file
+- WSS_WPG
Trying to login ………
Using current Windows Credentials
***** c2WTS could not provide a valid Windows Token. Reason: WTS0003: The caller is not authorized to access the service.
Server stack trace:
at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter)
at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc)
at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout)
at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation)
at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message)
Exception rethrown at [0]:
at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg)
at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation)
at c2WTSTest.Form1.button2_Click(Object sender, EventArgs e)
Now Verifying if user DOMAIN/monish has rights on c2WTS
+- User DOMAIN/monish has no access to the service
*** Analysis Complete ***
I also see that my domain account DOMAIN/monish was not added in WSS_WPG group. What do i need to do to resolve this?
Thanks -
Anonymous
January 01, 2013
The comment has been removed -
Anonymous
January 01, 2013
monish,
the service is not running in this machine. look for my post on c2wts dependencies. -
Anonymous
January 01, 2013
Thanks Rodney for the reply.
But I checked server manager, it shows c2wts is started. -
Anonymous
January 01, 2013
[adding more detail]
Thanks Rodney for reply.
I checked ‘Server manager’ and verified that c2wts and Cryptographic services both are already running/started. -
Anonymous
January 28, 2013
HI Rodney, Thanks for the post. I used the app to check if another user has rights. I gave his user id, UPN and his password. But got an error ” Token cannot be zero” , while i was the logged in user to the server. What may be wrong? Both of us are part of different domains. -
Anonymous
May 24, 2013
Even though this is the PowerPivot and Excel Services blog, I felt that adding a blog on this common -
Anonymous
May 27, 2013
Even though this is the PowerPivot and Excel Services blog, I felt that adding a blog on this common -
Anonymous
February 13, 2014
Superb write up of a complex problem.
Thank you very much. -
Anonymous
August 05, 2014
It is unclear to me whether ‘Claims to Windows Token Service’ can run under ‘Local System’ or whether it needs to be a different AD Account. We get this error in psiGen Migrate step after converting SP 2010 to Claims Based Authentication.
SPSecurityContext.WindowsIdentity: Could not retrieve a valid windows identity for NTName=’MYDOMAINMyuser’, UPN=’myuser@mydomian.com’. UPN is required when Kerberos constrained delegation is used. Exception: System.ServiceModel.FaultException`1[System.ServiceModel.ExceptionDetail]: WTS0003: The caller is not authorized to access the service. (Fault Detail is equal to An ExceptionDetail, likely created by IncludeExceptionDetailInFaults=true, whose value is: System.UnauthorizedAccessException: WTS0003: The caller is not authorized to access the service. -
Anonymous
January 21, 2015
When running the C2WTS service as a domain account, make sure it is present in the local administrator group on the application server or the servers that makes delegation (from Excel Services, Reporting Services etc.).
Add the account to the group and restart the service in Service Manager.
Resolved the error on a farm that I am administrator. -
Anonymous
March 08, 2015
Thank you! This article helped me! -
Anonymous
March 31, 2015
What kind of rights does a user need to have to executte this tool? I get
***** c2WTS could not provide a valid Windows Token. Reason: Access is denied.
+- User ***** has access rights per group/user WSS_WPG. Other groups will not be checked
When I run this tool as the farm account it works -
Anonymous
March 31, 2015
Hi Danny,
The user running c2WTS service may not have the appropriate rights. Look at this KB:
support.microsoft.com/…/2722087
Item 4 in special. -
Anonymous
March 31, 2015
Hi Rodney,
That article describes kerberos but my webapplication uses NTLM. So that doesn’t apply I think.
On another dev server in a different farm where I log in as a domain admin it does work.
Also another strange thing on the dev server that works.I have user danny@spdev.local with login name spdevdanny. In AD i see the UPN danny@spdev.local. With the tool I can test and it works. When I remove the UPN from the account the tool still finds this user with upn danny@spdev or danny@spdev.local how is this possible? When I check with for example ADExplorer I see that the account danny no longer has a upn -
Anonymous
April 01, 2015
The account that the c2wts service runs under has correct permissions according to the article (item 4). It seems that the account that starts the tool is missing some permissions. Any idea? -
Anonymous
April 02, 2015
Hi Danny,
There are some assumptions when it comes to upn: user@<domain-short> and user@<domain-full>. NTLM does not work with delegation.
If you followed the KB and still experience problems you may be running into a different issue which may be unrelated to c2WTS. See this post: blogs.msdn.com/…/verifying-whether-the-broken-piece-is-c2wts-or-active-directory.aspx -
Anonymous
April 06, 2015
Hi Rodney,
I am going to try your other test tool as all rights seem to be ok. The users that is starting the C2WTS tool doesn’t need any special rights?
The question about the UPN: When I use the tool ADExplorer I see that a UPN for a specific user is empty. But when running the C2WTS tester I can find that user on UPN. Is this normal? -
Anonymous
July 28, 2015
Hi Rodney,
I have SharePoint 2013, SQL Server 2012 SP1, SSRS on SharePoint Mode and PowerPivot add-in.
I am facing the issue with Power View when “PowerView” icon is clicked.I followed some of the instruction in the forum but still the problem is at large.
- The C2WTS Windows service and C2WTS SharePoint service are both running
- Checked the SQL Server Browser service is running on the machine that has the PowerPivot instance of SSAS.
- I have Claims Based Authentication on my farm.
Error code is as given below though it remain the same.Appreciate any help to fix the issue..
Regards
Sakti
<Message xmlns=”www.microsoft.com/…/reportingservices”>An error occurred while loading the model for the item or data source ‘abcd.abcd.com/…/QA-SSAS.xlsx&. Verify that the connection information is correct and that you have permissions to access the data source.
mlns:msrs=”www.microsoft.com/…/reportingservices”>An error occurred while loading the model for the item or data source ‘abcd.abcd.com/…/QA-SSAS.xlsx&. Verify that the connection information is correct and that you have permissions to access the datasource.</Message>
“xmlns:msrs=”www.microsoft.com/…/reportingservices”>Cannot create a connection to datasource ‘TemporaryDataSource’.<Message>Call to Excel Services returned an error.We’re sorry. We ran into a problem completing your request.<Message>We’re sorry. We ran into a problem completing your request.</Message>
- Anonymous
March 21, 2016
I installed and ran the utility – Excellent! Some users work fine, others get “c2WTS could not provide a valid Windows Token. Reason: Access is denied.” So, if it isn’t c2WTS, then what is it? Permissions on AD? What do I need to change?here is the error message:Testing Service c2WTS +- Service c2WTS found +- Service c2WTS is running +- Path of service: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe +- Config File: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe.config +- Service Logon: _SPAdminDev\XYZ*** Service MUST BE ‘SYSTEM\NT AUTHORITY’ —– start of config file —- —– end of config file —-Retrieving security groups/users allowed to use the service from config file +- WSS_WPGTrying to login ………Using provided credentials to login** c2WTS could not provide a valid Windows Token. Reason: Access is denied.Server stack trace: at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter) at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc) at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout) at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation) at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message)Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.c__DisplayClass1.b__0(IS4UService_dup channel) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation) at c2WTSTest.Form1.button2_Click(Object sender, EventArgs e)Now Verifying if user XYZ_SPAdminDev has rights on c2WTS +- User XYZ_SPAdminDev has access rights per group/user WSS_WPG. Other groups will not be checked*** Analysis Complete ***- Anonymous
April 06, 2016
Check this other post: https://blogs.msdn.microsoft.com/rodneyviana/2014/03/21/verifying-whether-the-broken-piece-is-c2wts-or-active-directory/Run the application from the post as XYZ_SPAdminDev and see if it can resolve the upn. If not it is AD related and the error will be more specific.
- Anonymous
- Anonymous
July 26, 2016
The comment has been removed - Anonymous
April 13, 2017
You might want to move the EXE for future use since Codeplex is about to be shut down. - Anonymous
June 14, 2017
My issue seems to be the that the UPN cannot be converted to a windows identity When i Run your app and click on “get UPN for logged user” it returns USERNAME@DOMAIN and this works to get the windows identity but if i run whoami/UPN I get : Name.lastname@Domain.Com that is different from the one i use to login when i run the app with this UPN I get : c2WTS could not provide a valid Windows Token. Reason: Access is denied.Server stack trace: at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter) at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc) at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout) at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation) at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message)Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.c__DisplayClass1.b__0(IS4UService_dup channel) at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation) at c2WTSTest.Form1.button2_Click(Object sender, EventArgs e)when I go to the ULS logs i see : Could not retrieve a valid windows identity for NTName=’Domain\USERNAME’, UPN=’Name.LastName@DOMAIN.com’. UPN is required when Kerberos constrained delegation is used. Exception: System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. This only happens with the users trying to connect from a trusted Domain, the users from the local domain have no issues as the UPN and the Claims look the same. My C2WTS is running as Local system
I have been writing some blogs entries (and even a Microsoft KB) about c2WTS, but the subject never exhausts. I was helping two different customers to troubleshoot issues with SharePoint Excel Services. In one of the cases the problem happened randomly and the error message was saying that the request to the external data (SQL) had failed because the request did not include a valid Kerberos header, but no reference to c2WTS in the ULS logs.
The other case was that some users could access Excel Services while others could not, this time there was an error in ULS logs pointing to access denied in c2WTS. Without explaining the internals of these two cases, one can say that in both cases c2WTS was working as expected but some other factor was impairing its use with SharePoint.
Before pointing at c2WTS as culprit of some SharePoint access error, look for these three tags in the ULS logs: g8g7, fvx8 or bz7l in Claims Authentication category (Medium).
This ULS entry would look like this:
07/14/2011 14:33:34.03 w3wp.exe (0x1144)0x1960 SharePoint Foundation Claims Authentication bz7l Medium
SPSecurityContext.WindowsIdentity: Could not retrieve a valid windows identity for NTName=’CONTOSO\jdoed’, UPN=’jdoed@contoso.com’. UPN is required when Kerberos constrained delegation is used. Exception: System.ServiceModel.Security.SecurityAccessDeniedException: Access is denied. Server stack trace:
at System.ServiceModel.Channels.ServiceChannel.ThrowIfFaultUnderstood(Message reply, MessageFault fault, String action, MessageVersion version, FaultConverter faultConverter)
at System.ServiceModel.Channels.ServiceChannel.HandleReply(ProxyOperationRuntime operation, ProxyRpc& rpc)
at System.ServiceModel.Channels.ServiceChannel.Call(String action, Boolean oneway, ProxyOperationRuntime operation, Object[] ins, Object[] outs, TimeSpan timeout)
at System.ServiceModel.Channels.ServiceChannelProxy.InvokeService(IMethodCallMessage methodCall, ProxyOperationRuntime operation)
at System.ServiceModel.Channels.ServiceChannelProxy.Invoke(IMessage message) Exception rethrown
at [0]:
at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg)
at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.IS4UService_dup.UpnLogon(String upn, Int32 pid)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.<>c__DisplayClass1.<UpnLogon>b__0(IS4UService_dup channel)
at Microsoft.IdentityModel.WindowsTokenService.S4UClient.CallService(Func`2 contractOperation)
at Microsoft.SharePoint.SPSecurityContext.GetWindowsIdentity().
SharePoint uses c2WTS to transform a claim identity into a valid Windows Identity Token. You cannot (for now) send a request to SQL Server or other data sources passing the claim. So, for internal users in Active Directory the claim will be mapped to a Windows Identity Token and that token will be used to access the resource. Since c2WTS only requires the UPN to generate a token, by default no one can access the service. To allow access you have to edit the .config file to add the groups and users to the allowed callers section.
SharePoint installs c2WTS as part of its pre-requisites as c2WTS is actually part of Windows Identity Foundation SDK. The configuration happens when you add the correspondent service in the farm. If everything is alright the service will be configured to start automatically (read my previous post on dependencies) under SYSTEM\NT AUTHORITY and will add the SharePoint local group WSS_WPG to the list of allowed groups in c2WTS. When adding SharePoint Excel Services, the domain account provided needs to be able to create Windows tokens in the c2WTS machine (the service only works with local requests) and it will be added automatically to WSS_WPG by SharePoint (you don’t have to do this). All this actions are necessary since once accessing the service you can impersonate a user by simply supplying the UPN claim. The input is the UPN string. The return is the (limited) Windows Token or an error.
Testing c2WTS configuration is not possible without some code. You have to be logged (or impersonating) an account that has rights to c2WTS. I suggest the account you used for Excel Services. To test using the same method that SharePoint does, you only need to call this static class in c2WTS:
WindowsIdentity wi = S4UClient.UpnLogon(“rviana@contoso.com”);
This static method will use WCF net.pipe (only local) to communicate with the real c2WTS service (I blogged about net.pipe and real pipes in a previous post). The full test of the complete configuration is a bit more complex. I have put together a sample application to perform all tests I could remember. The App looks like:
Quick Instructions:
Start the Application as Administrator. If you want to impersonate Excel Account, change “User Login” to enable the Password field. By default the user will be the account running the application. If you want to continue with the interactive user, you will not need to enter password. For UPN you can enter any valid UPN claim (normally user@domain), if you want to test your own account you can choose to get UPN from logged user. If you want to impersonate another user or test if the current user can obtain tokens, please enter the UPN manually.
Full Result:
| Testing Service c2WTS+- Service c2WTS found+- Service c2WTS is running+- Path of service: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe+- Config File: C:\Program Files\Windows Identity Foundation\v3.5\c2wtshost.exe.config+- Service Logon: SYSTEM\NT AUTHORITY—– start of config file —-<?xml version=”1.0″?><configuration><configSections><section name=”windowsTokenService” type=”Microsoft.IdentityModel.WindowsTokenService.Configuration.WindowsTokenServiceSection, Microsoft.IdentityModel.WindowsTokenService, Version=3.5.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35″ /></configSections><startup><supportedRuntime version=”v4.0″ /><supportedRuntime version=”v2.0.50727″ /></startup><windowsTokenService><!–By default no callers are allowed to use the Windows Identity Foundation Claims To NT Token Service.Add the identities you wish to allow below.–><allowedCallers><clear /><add value=”WSS_WPG” /></allowedCallers></windowsTokenService></configuration>—– end of config file —-Retrieving security groups/users allowed to use the service from config file+- WSS_WPGTrying to login ………Using current Windows Credentialsc2WTS Service provided a valid Windows Token for: CONTOSO\cpajaroNow Verifying if user CONTOSO\rviana has rights on c2WTS+- User CONTOSO\rviana has access rights per group/user WSS_WPG. Other groups will not be checked*** Analysis Complete *** |
You can download source and EXE here.
Please notice that since this is supposed to mimic SharePoint 2010, the App is 64-bits. Also be aware this application is provided “AS IS” with no guarantees. You need to accept the license to use it.